Protect Yourself From Vishing Scams
Posted on Apr 30, 2026

Phone-based scams, also known as vishing, are becoming increasingly common across financial institutions. Unlike email-based attacks, these rely on real-time conversation to build trust, create urgency, and influence decisions quickly.
A single phone interaction, if not handled carefully, can result in unauthorized access, system compromise, or exposure of sensitive information.
What is Vishing?
Vishing (voice phishing) is a type of social engineering where attackers call individuals pretending to be trusted sources, such as IT support, vendors, or internal employees. Their goal is to persuade you to take action, such as installing software, sharing credentials, or granting access.
These attackers often prepare in advance by gathering publicly available information, making their story sound believable and relevant.
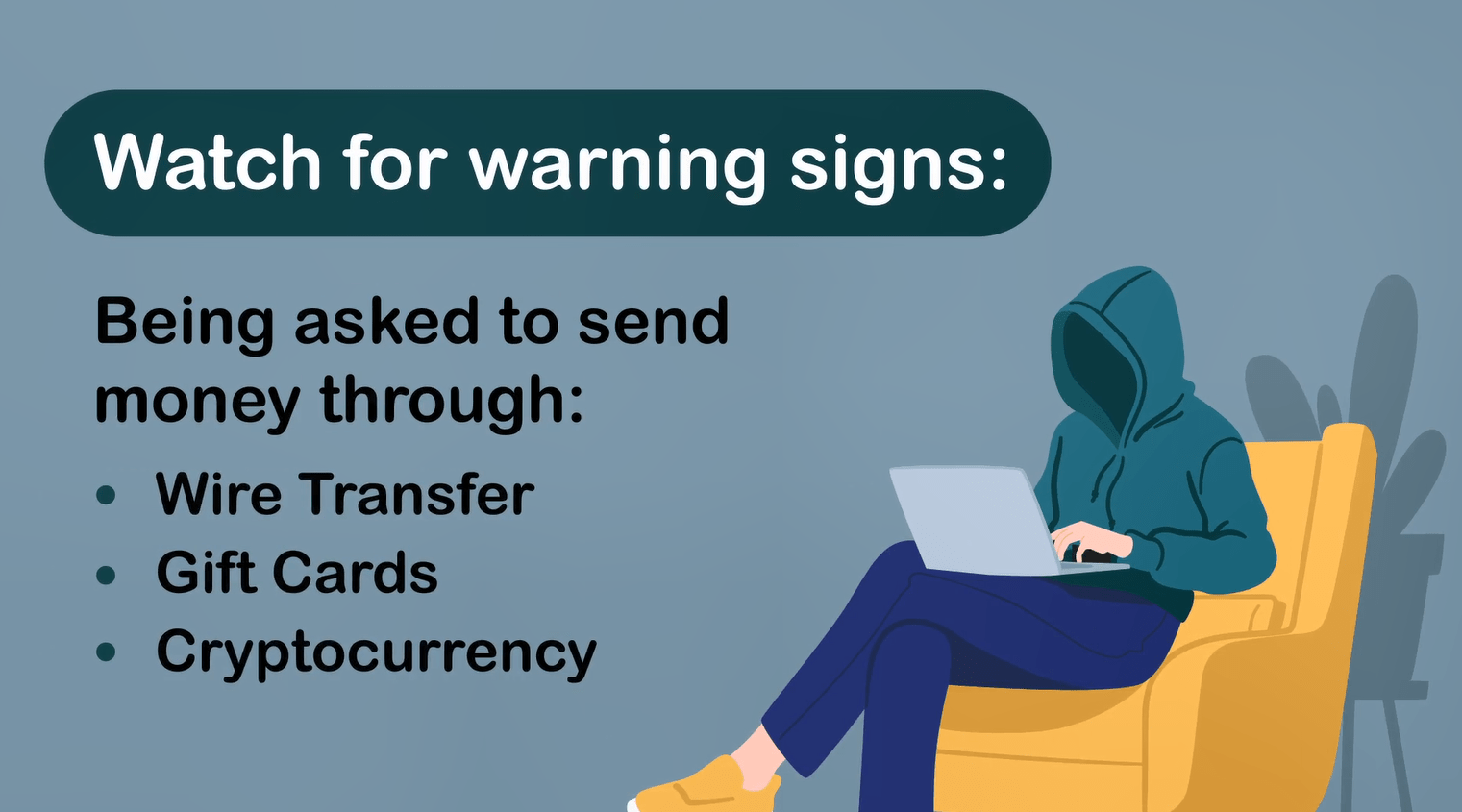
Common Red Flags
- The caller creates urgency or pressure (e.g., “this must be fixed immediately”)
- Requests to install software, grant access, or bypass normal procedures
- Asks for passwords, MFA codes, or sensitive information
- Uses vague explanations or inconsistent details
- Repeated calls or attempts to keep you on the line
- Caller ID appears legitimate, but behavior or request feels unusual
Why It Works
Vishing is effective because it targets human behavior. In a live conversation, it’s harder to pause and evaluate the situation. Attackers rely on urgency and authority to push quick decisions, often before there’s time to verify.
They may also use real employee names or internal language to make the request feel more legitimate.
Real-World Scenario
You receive a call from someone claiming to be from IT. They explain that you missed a required update and your system may stop working if it’s not fixed immediately. They offer to walk you through installing a tool or request access to your system.
What You Should Do
- Do not follow instructions from unsolicited callers
- Never install software or provide access based on a phone request
- Do not share passwords, MFA codes, or credentials
- Politely end the call
- Contact the Helpdesk directly using official channels
- Report the incident so others can be alerted
Why This Matters to FHB
Phone-based attacks bypass many traditional security controls. Protecting against them depends on employee awareness and the ability to pause, question, and verify.
Key Takeaway
Trust, but always verify.
If something feels off, pause the conversation and confirm through official channels.
Was this helpful?
Thank you for the feedback